Tigerexch Login & Signup Guide 2026 – Fast Access & Secure ID
Introduction
In the rapidly evolving world of cryptocurrency trading, speed and security are two non‑negotiable pillars for any successful exchange platform. As we step into 2026, Tigerexch has positioned itself as a leader by offering a streamlined onboarding experience that balances instant access with robust identity protection. Whether you are a seasoned trader looking to migrate accounts or a newcomer eager to explore digital assets, understanding the exact steps to log in and create a new account will save you time and reduce friction. This guide dissects every part of the process, from the moment you land on the homepage to the final verification checkpoint, ensuring you can navigate the platform with confidence.
Why a Dedicated Guide Matters in 2026
Cryptocurrency exchanges continuously adapt to regulatory changes, emerging security threats, and user‑experience innovations. Tigerexch’s 2026 interface reflects these trends through multi‑factor authentication, biometric options, and AI‑driven fraud detection. However, the richness of these features can sometimes overwhelm users who are unfamiliar with the latest standards. A dedicated guide eliminates guesswork, minimizes the risk of account lockouts, and helps you leverage every security tool available. Moreover, by following a proven workflow, you align your actions with best‑practice compliance, which is especially vital for traders dealing with high‑volume or institutional funds.
Step‑by‑Step Login Process
1. Access the Official Login Portal
Begin by opening your preferred web browser and navigating to the Tigerexch homepage. Locate the “Login” button positioned at the top‑right corner of the navigation bar. Clicking this button redirects you to a secure SSL‑encrypted login page. The URL will start with “https://” and display a padlock icon, confirming a safe connection.
2. Enter Your Credentials
Input the email address you used during registration and the corresponding password. Tigerexch enforces a minimum password length of 12 characters, including at least one uppercase letter, one lowercase letter, a numeral, and a special character. Avoid common patterns or dictionary words to reduce vulnerability to brute‑force attacks.
3. Complete Multi‑Factor Authentication (MFA)
After submitting your credentials, the platform automatically triggers the MFA step. You can choose between an authenticator app (such as Google Authenticator or Authy), an SMS code, or a hardware security key (U2F). For maximum security, the hardware key option is recommended, as it is resistant to phishing and phishing‑resistant by design. Enter the generated code or tap your security key when prompted.
4. Review Session Details
Upon successful MFA verification, you will be presented with a session summary, including the IP address, device type, and approximate geolocation of the login attempt. If anything looks unfamiliar, you can terminate the session immediately and initiate a password reset. Otherwise, click “Continue to Dashboard” to access your account.
Creating a New Account (Signup)
1. Locate the “Sign Up” Button
If you are a first‑time visitor, the homepage features a prominent “Sign Up” call‑to‑action next to the login link. Clicking it opens the registration form, which is designed to be mobile‑responsive for users on smartphones or tablets.
2. Provide Basic Personal Information
The form requires your full legal name, a valid email address, and a mobile phone number capable of receiving SMS messages. Ensure that the email you provide is one you regularly monitor, as it will be the primary channel for account notifications, security alerts, and future password recovery.
3. Set a Strong Password
Follow the same complexity rules used for login passwords. The platform offers a real‑time strength meter that guides you through the creation of a resilient password. Consider using a reputable password manager to generate and store this credential securely.
4. Agree to Terms and Privacy Policy
Review the updated Terms of Service and Privacy Policy—both have been revised in early 2026 to incorporate new data‑protection standards such as GDPR‑like provisions for Indian users. Check the acceptance box only after you understand the obligations and rights outlined.
5. Initiate Email Verification
Once the form is submitted, an automated verification email is dispatched to the address you entered. Click the unique verification link inside the email within 24 hours; otherwise, the registration will expire, and you will need to restart the process.
Identity Verification (KYC) – The Secure ID Backbone
After your email is confirmed, Tigerexch requires you to complete a Know‑Your‑Customer (KYC) verification to unlock full trading functionalities. The KYC workflow in 2026 has been refined to reduce friction while complying with anti‑money‑laundering (AML) regulations. Begin by uploading a clear, color photograph of a government‑issued ID (e.g., PAN card, Aadhaar card, or passport). Next, submit a selfie holding the ID next to your face, ensuring that both documents are legible and the lighting is adequate. Tigerexch’s AI‑driven verification engine will cross‑check the data within seconds, returning a “verified” status typically within 5‑10 minutes. If manual review is required, you will receive an email outlining the missing or unclear elements, and you can re‑upload the documents accordingly.
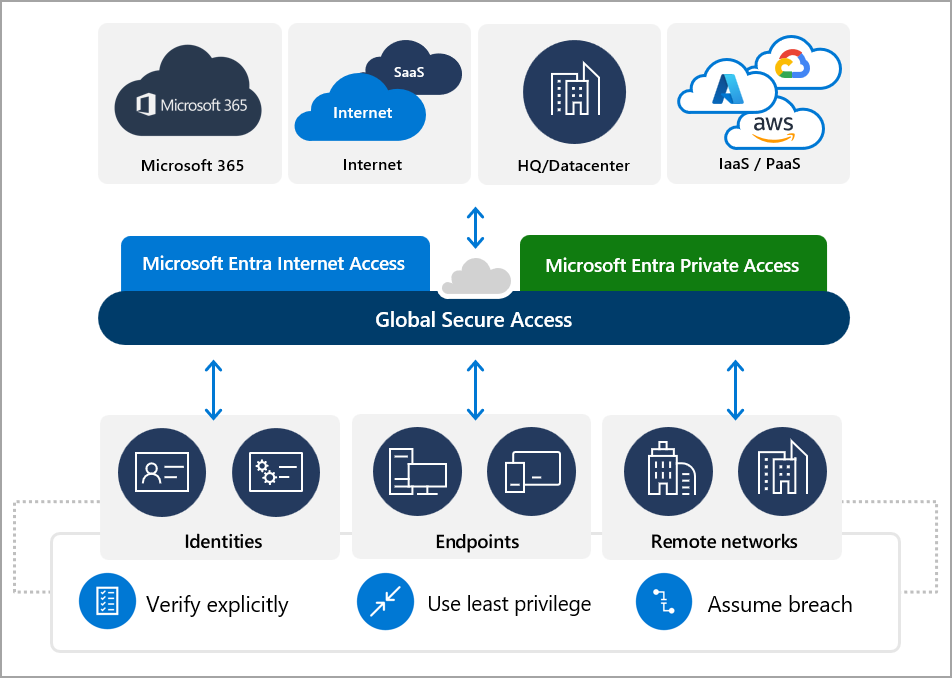
Security Features that Define the 2026 Experience
The platform integrates several layers of defense to protect user assets and personal data. First, the hardware‑rooted encryption of all stored credentials ensures that even a server breach would not expose passwords in clear text. Second, continuous monitoring powered by machine learning detects anomalous login patterns, such as logins from unfamiliar geographic regions or rapid successive attempts, and can automatically lock the account pending user confirmation. Third, a built‑in withdrawal whitelist allows users to pre‑authorize specific wallet addresses, preventing unauthorized fund transfers. Finally, Tigerexch offers optional biometric login via fingerprint or facial recognition on supported devices, creating a frictionless yet secure entry point.
Managing Devices and Sessions
Control over active devices is crucial for maintaining a secure digital footprint. Within the “Security Settings” tab of your dashboard, you can view a list of all devices that have authenticated sessions, complete with timestamps, IP addresses, and device identifiers. Should you notice an unfamiliar device, you can instantly terminate its session and force a password reset. Additionally, you can enable “Session Timeout” to automatically log you out after a predefined period of inactivity, further reducing the attack surface.
Troubleshooting Common Issues
Forgotten Password: Click the “Forgot Password?” link on the login page. Provide your registered email, and a password‑reset link will be sent. Use a new password that complies with the platform’s complexity requirements.
Failed MFA Prompt: Verify that the time on your authenticator app is synchronized; most apps have a “time sync” option in their settings. If using SMS, ensure your mobile carrier is not blocking short‑code messages. For hardware keys, check that the USB or NFC connection is functional.
Verification Email Not Received: Check your spam or promotions folder. Add [email protected] to your contacts list. If still missing, request a new verification email from the login screen.
KYC Rejection: Review the rejection email for specific reasons. Common issues include blurred images, mismatched names, or expired IDs. Resubmit high‑resolution photos that meet the stipulated criteria.
Best Practices for a Seamless 2026 Experience
Adhering to a few disciplined habits can dramatically improve both security and usability. Always keep your operating system and browser up to date to benefit from the latest security patches. Use a dedicated password manager to generate unique passwords for each service, and store your MFA recovery codes in a secure offline location. Regularly review the “Withdrawal Whitelist” and prune any addresses you no longer use. Finally, stay informed about platform updates by subscribing to Tigerexch’s official newsletters; major changes—such as new authentication methods or policy revisions—are typically announced well in advance.
Frequently Asked Questions (FAQ)
Q: Can I use the same email for multiple accounts?
A: No. Tigerexch enforces a one‑to‑one relationship between an email address and an account to prevent fraud and simplify KYC compliance.
Q: Is the mobile app identical to the web platform in terms of security?
A: Yes. The mobile application employs the same encryption standards, MFA options, and withdrawal whitelist controls as the desktop version.
Q: How long does KYC verification take?
A: Automated verification usually completes within 5‑10 minutes. Manual review, if required, may take up to 24 hours.
Q: What should I do if I suspect my account has been compromised?
A: Immediately log out from all devices via the “Security Settings” page, change your password, and contact Tigerexch support with a detailed description of the incident.
Conclusion
Mastering the login and signup workflow on Tigerexch in 2026 is less about memorizing steps and more about embracing a security‑first mindset. By following the structured process outlined above—starting from the initial navigation to the final KYC approval—you position yourself for fast, reliable access to one of the most secure cryptocurrency exchanges available today. Remember to regularly audit your security settings, stay current with platform updates, and leverage the full suite of MFA and biometric tools at your disposal. With these practices in place, you can focus on what matters most: executing trades, managing assets, and capitalizing on the dynamic opportunities that the digital asset market presents.